Search results
Appearance
There is a page named "Brute-force attacks" on Wikipedia
- a brute-force attack consists of an attacker submitting many passwords or passphrases with the hope of eventually guessing correctly. The attacker systematically...21 KB (2,250 words) - 15:26, 19 July 2024
- In computer science, brute-force search or exhaustive search, also known as generate and test, is a very general problem-solving technique and algorithmic...14 KB (1,964 words) - 14:50, 6 March 2024
- Look up brute force in Wiktionary, the free dictionary. Brute Force or brute force may refer to: Brute force method or proof by exhaustion, a method of...1 KB (211 words) - 06:46, 9 March 2023
- Key size (section Brute-force attack)of the fastest known attack against an algorithm), because the security of all algorithms can be violated by brute-force attacks. Ideally, the lower-bound...29 KB (3,213 words) - 18:51, 7 June 2024
- with a sliding computational cost, used to reduce vulnerability to brute-force attacks. PBKDF2 is part of RSA Laboratories' Public-Key Cryptography Standards...13 KB (1,341 words) - 15:37, 30 May 2024
- (strengthened against differential cryptanalysis, but weakened against brute-force attacks), which was published as an official Federal Information Processing...59 KB (6,541 words) - 19:15, 14 April 2024
- flaw that makes brute-force attacks against PIN-based WPS feasible to be performed on WPS-enabled Wi-Fi networks. A successful attack on WPS allows unauthorized...20 KB (2,647 words) - 07:31, 10 July 2024
- Rainbow table (redirect from Rainbow attack)into the hash function, creates that same hash. Though brute-force attacks (e.g. dictionary attacks) may be used to try to invert a hash function, they can...24 KB (3,446 words) - 08:05, 23 June 2024
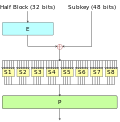
- Block cipher (section Brute-force attacks)block cipher must be secure, in addition to being robust against brute-force attacks. Most block cipher algorithms are classified as iterated block ciphers...50 KB (6,475 words) - 10:19, 23 June 2024
- Fail2ban (category Brute force blocking software)Written in the Python programming language, it is designed to prevent brute-force attacks. It is able to run on POSIX systems that have an interface to a packet-control...8 KB (717 words) - 08:32, 24 April 2024
- the previous example. A de Bruijn sequence can be used to shorten a brute-force attack on a PIN-like code lock that does not have an "enter" key and accepts...32 KB (3,517 words) - 03:20, 25 March 2024
- time, increases in processor speeds since the PDP-11 era have made brute-force attacks against crypt feasible, and advances in storage have rendered the...13 KB (1,625 words) - 12:36, 12 July 2024
- longer—20 to 30 characters or more is typical—making some kinds of brute force attacks entirely impractical. Second, if well chosen, they will not be found...12 KB (1,613 words) - 01:42, 10 June 2024
- are vulnerable to brute force attacks, every cryptographic hash function is inherently vulnerable to collisions using a birthday attack. Due to the birthday...17 KB (2,010 words) - 21:48, 17 May 2024
- of a password against guessing or brute-force attacks. In its usual form, it estimates how many trials an attacker who does not have direct access to...57 KB (6,264 words) - 11:03, 12 July 2024
- to compute a first or second preimage is through a brute-force attack. For an n-bit hash, this attack has a time complexity 2n, which is considered too...7 KB (895 words) - 15:44, 13 April 2024
- Password cracking (category Cryptographic attacks)attacks, pattern checking, and variations of common words, aim to optimize the number of guesses and are usually attempted before brute-force attacks...27 KB (3,107 words) - 18:58, 18 July 2024
- addresses. IP address blocking is commonly used to protect against brute force attacks and to prevent access by a disruptive address. It can also be used...7 KB (868 words) - 12:14, 7 May 2024
- environments. Hydra works by using different approaches to perform brute-force attacks in order to guess the right username and password combination. Hydra...3 KB (191 words) - 00:49, 7 March 2023
- Return-oriented programming (section Attacks)dramatically increase software's immunity to ROP attacks. Brute forcing Cloud Lambda may result in attacking several instances of the randomized software...31 KB (3,847 words) - 08:53, 28 May 2024
- The Abysmal Brute by Jack London 137433The Abysmal BruteJack London The consummation of his career was rapidly approaching. The great champion had even
- Terrorism (redirect from Terrorist attacks)Studies, (June 3, 2020). We cannot lose to terrorism, we must not yield to brute force. Junichirō Koizumi, as quoted in "Beheaded Japanese to be flown home"
- A brute force attack against a cipher consists of breaking a cipher by trying all possible keys. Statistically, if the keys were originally chosen randomly