Search results
Appearance
There is a page named "Biclique attack" on Wikipedia
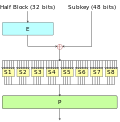
- A biclique attack is a variant of the meet-in-the-middle (MITM) method of cryptanalysis. It utilizes a biclique structure to extend the number of possibly...18 KB (3,173 words) - 22:38, 29 October 2023
- Advanced Encryption Standard (section Known attacks)Khovratovich, and Christian Rechberger, and were published in 2011. The attack is a biclique attack and is faster than brute force by a factor of about four. It...49 KB (5,600 words) - 21:31, 14 June 2024
- Complete bipartite graph (redirect from Biclique)the mathematical field of graph theory, a complete bipartite graph or biclique is a special kind of bipartite graph where every vertex of the first set...12 KB (959 words) - 06:10, 4 July 2022
- brute-force attack consists of an attacker submitting many passwords or passphrases with the hope of eventually guessing correctly. The attacker systematically...20 KB (2,205 words) - 18:26, 19 June 2024
- In cryptography, a timing attack is a side-channel attack in which the attacker attempts to compromise a cryptosystem by analyzing the time taken to execute...12 KB (1,524 words) - 16:53, 11 May 2024
- using a meet-in-the-middle attack. Independently in 2012, full 8.5-round IDEA was broken using a narrow-bicliques attack, with a reduction of cryptographic...12 KB (1,499 words) - 19:07, 14 April 2024
- Cipher security summary (section Best attack)Andrey Bogdanov; Dmitry Khovratovich; Christian Rechberger (2011-08-17). "Biclique Cryptanalysis of the Full AES". Cryptology ePrint Archive. Vincent Rijmen...15 KB (801 words) - 20:43, 9 June 2024
- In cryptography, a related-key attack is any form of cryptanalysis where the attacker can observe the operation of a cipher under several different keys...5 KB (688 words) - 07:27, 20 November 2023
- Differential cryptanalysis (redirect from Differential attack)resistant to this attack and many including the Advanced Encryption Standard, have been proven secure against the attack. The attack relies primarily on...13 KB (1,688 words) - 22:44, 29 October 2023
- successful attack.[citation needed] It is also possible to increase the key length or the rounds in the encryption process to better protect against attack. This...15 KB (1,544 words) - 02:53, 7 June 2024
- number of platforms. Käsper and Schwabe described a "Faster and Timing-Attack Resistant AES-GCM" that achieves 10.68 cycles per byte AES-GCM authenticated...23 KB (2,999 words) - 05:42, 12 June 2024
- Block cipher (section Brute-force attacks)of 2012[update], the best attack which applies to all keys can break a full 8.5-round IDEA using a narrow-bicliques attack about four times faster than...50 KB (6,475 words) - 22:23, 3 May 2024
- Data Encryption Standard (section Brute-force attack)(strengthened against differential cryptanalysis, but weakened against brute-force attacks), which was published as an official Federal Information Processing Standard...59 KB (6,541 words) - 19:15, 14 April 2024
- Correlation attacks are a class of cryptographic known-plaintext attacks for breaking stream ciphers whose keystreams are generated by combining the output...15 KB (2,299 words) - 10:31, 29 January 2024
- is encrypted multiple times with the same nonce. When that happens, an attacker is able to observe repeat encryptions, since encryption is a deterministic...3 KB (382 words) - 16:11, 7 February 2024
- The slide attack is a form of cryptanalysis designed to deal with the prevailing idea that even weak ciphers can become very strong by increasing the number...7 KB (1,135 words) - 08:49, 25 July 2023
- (Whitening transformation) Attack (cryptanalysis) Brute-force (EFF DES cracker) MITM Biclique attack 3-subset MITM attack Linear (Piling-up lemma) Differential...8 KB (848 words) - 03:29, 28 April 2024
- 64-bit block size and therefore it could be vulnerable to Sweet32 birthday attacks. Schneier designed Blowfish as a general-purpose algorithm, intended as...16 KB (1,807 words) - 09:50, 20 June 2024
- independent key bits. It is still vulnerable to the meet-in-the-middle attack, but the attack requires 22 × 56 steps. Keying option 2 K1 and K2 are independent...23 KB (2,946 words) - 08:25, 17 May 2024
- susceptible to padding oracle attacks. Padding oracle attacks allow the attacker to gain knowledge of the plain text without attacking the block cipher primitive...23 KB (3,307 words) - 18:11, 14 February 2024